Not known Facts About Risk Management Enterprise
Unknown Facts About Risk Management Enterprise
Table of ContentsHow Risk Management Enterprise can Save You Time, Stress, and Money.7 Simple Techniques For Risk Management EnterpriseThe Definitive Guide to Risk Management Enterprise5 Simple Techniques For Risk Management EnterpriseThe smart Trick of Risk Management Enterprise That Nobody is Talking AboutThe Best Strategy To Use For Risk Management EnterpriseThe Greatest Guide To Risk Management Enterprise
Right here are some of its crucial attributes that facilities should understand. Take an appearance. Real-Time Danger Assessments and Mitigation in this software permit organizations to continually keep an eye on and review risks as they develop. This feature leverages real-time data and automatic evaluation to recognize possible threats quickly. When risks are determined, the software application promotes immediate mitigation activities.
They address the obstacle of recurring danger monitoring by offering tools to keep an eye on risks continuously. KRIs improve safety and security risk oversight, guaranteeing that prospective dangers are determined and handled effectively.
Risk Management Enterprise for Dummies
IT run the risk of administration is a subset of enterprise danger management (ERM), developed to bring IT run the risk of in accordance with a company's danger cravings. IT run the risk of administration (ITRM) encompasses the plans, treatments and innovation necessary to reduce risks and vulnerabilities, while keeping compliance with relevant regulative requirements. On top of that, ITRM looks for to restrict the consequences of harmful events, such as safety and security breaches.
While ITRM frameworks provide helpful support, it's simple for IT teams to deal with "structure overload." Veronica Rose, ISACA board supervisor and a details systems auditor at Metropol Corp. Ltd., suggests using a combination of frameworks to accomplish the ideal results. The ISACA Danger IT structure aligns well with the COBIT 2019 framework, Rose claimed.
Business Threat Administration Software Development: Advantages & Characteristics, Price. With technological developments, risks are constantly on the rise., companies navigate via a frequently changing sea of dangers.
Risk Management Enterprise Fundamentals Explained
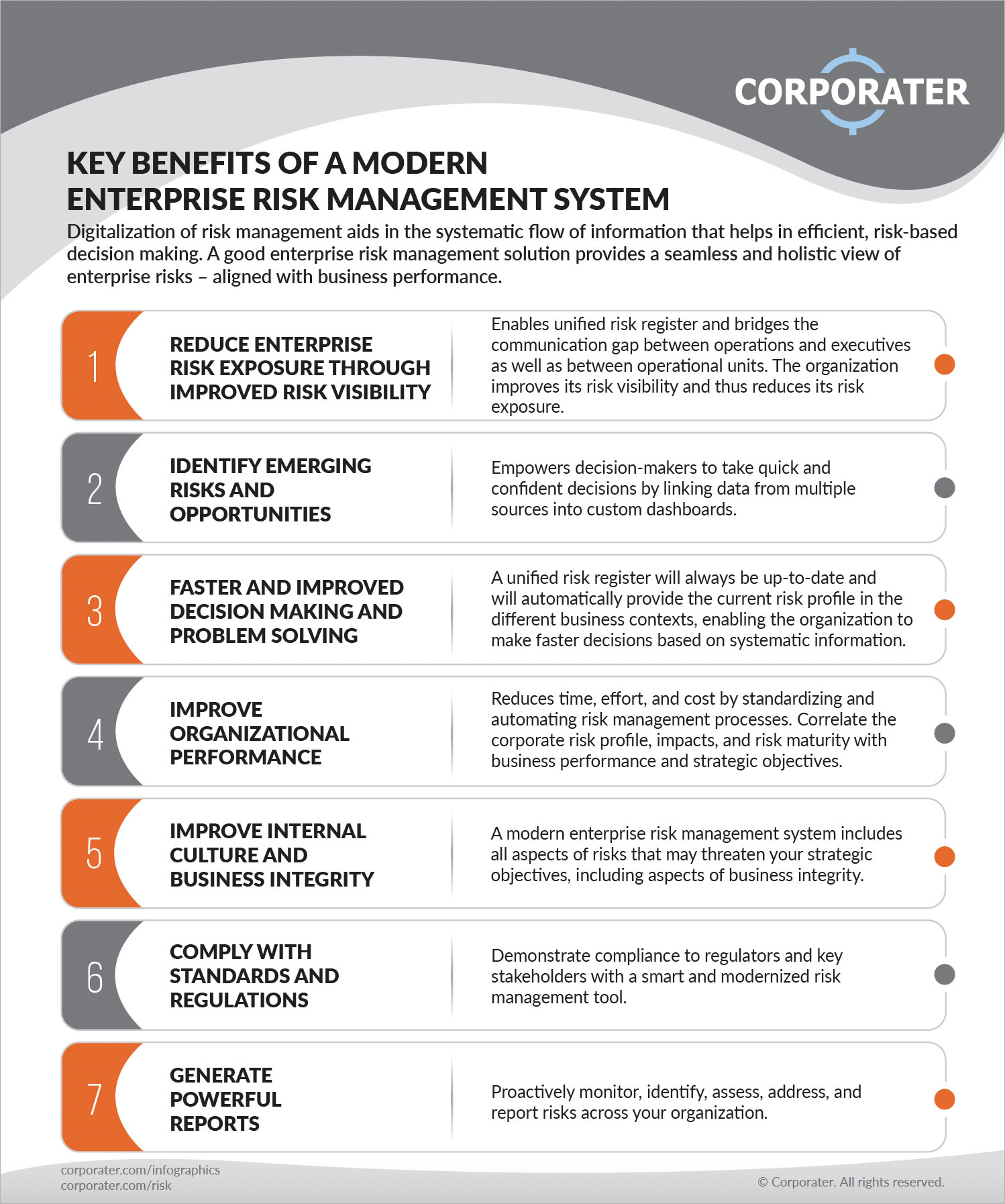
In this blog site, we will study the world of ERM software, discovering what it is, its benefits, functions, and so on so that you can develop one for your business. Venture Threat Management (ERM) software program is the application program for preparation, routing, arranging, and controlling company activities and streamlining risk management processes.
With ERM, companies can make informative decisions to enhance the total resilience of the service. Read: ERP Application Development Dedicated ERM systems are critical for businesses that frequently deal with huge amounts of delicate details and multiple stakeholders to accept calculated decisions. Some industries where ERM has actually ended up being a common system are healthcare, financing, building and construction, insurance coverage, and information modern technology (IT).
: It is difficult for any kind of venture to undertake an extensive audit. It can be stayed clear of by making use of the ERM software application system. This system automates guideline compliance monitoring to maintain the company safe and compliant. Aside from that, it likewise logs and categorizes all the data in the system making it much easier for auditors to assess processes a lot faster.
10 Easy Facts About Risk Management Enterprise Explained
You can likewise link existing software application systems to the ERM through APIs or by adding information by hand. Businesses can use ERM to review risks based on their potential effect for much better threat administration and mitigation.: Adding this function permits users to get real-time alerts on their tools regarding any kind of risk that could occur and its effect.
Instead, the software enables them to set limits for different procedures and send push alerts in situation of possible threats.: By integrating information visualization and reporting in the personalized ERM software program, services can gain clear insights about risk fads and performance.: It is obligatory for organizations to adhere to market compliance and regulatory requirements.
These systems enable companies to execute best-practice danger management procedures that align with market requirements, providing an effective, technology-driven approach to recognizing, assessing, and mitigating dangers. This blog explores the benefits of automatic threat monitoring tools, the locations of risk management they can automate, and the worth they give a company.
Risk Management Enterprise for Dummies
Groups can establish forms with the appropriate areas and quickly develop different kinds for different threat kinds. These risk assessment types can be circulated for completion using automated operations that send out notices to the pertinent personnel to complete the forms online. If forms are not finished by the due date, then chaser e-mails are automatically sent by the system.
The control monitoring and control screening procedure can additionally be automated. Companies can utilize automated workflows to send normal control test notices and staff can enter the outcomes using on the internet forms. Controls can additionally be monitored by the software program by setting rules to send out alerts based on control data kept in other systems and spreadsheets that is pulled right into the system by means of API integrations.
Danger monitoring automation software application can also support with threat coverage for all degrees of the enterprise. Leaders can view reports on risk exposure and control Find Out More performance via a selection of reporting outcomes consisting of static reports, Power BI interactive records, bowtie evaluation, and Monte Carlo simulations. The ability to draw live records at the touch of a switch cuts out arduous information adjustment tasks leaving threat groups with more time to examine the data and encourage the company on the most effective strategy.
Organizations operating in affordable, fast-changing markets can not afford delays or ineffectiveness in addressing prospective dangers. Standard danger monitoring utilizing hand-operated spreadsheet-based procedures, while familiar, commonly lead to fragmented data, taxing reporting, and an enhanced possibility of human mistake.
Getting My Risk Management Enterprise To Work
This guarantees risk signs up are constantly present and lined up with organizational goals. Conformity is an additional essential vehicle driver for automating threat administration. Requirements like ISO 31000, CPS 230 and COSO all provide guidance around threat management best practices and control frameworks, and automated risk management devices are structured to line up with these requirements helping companies to satisfy most typically used threat administration requirements.
Try to find threat software application systems with a consents pecking order to conveniently establish operations for threat escalation. This capability enables you to tailor the view for each customer, so they just see the data appropriate to them. Make sure the ERM software application provides customer monitoring so you can see who entered what information and when.
Seek out devices that offer task risk management abilities to handle your projects and profiles and the associated dangers. The benefits of embracing risk monitoring automation software application prolong much past performance.

The Risk Management Enterprise Diaries
While the case for automation is compelling, applying a risk administration platform is not without its obstacles. To conquer the difficulties of risk monitoring automation, companies must invest in information cleaning and administration to ensure a strong structure for applying an automated platform.
Automation in image source risk administration empowers businesses to change their technique to take the chance of and build a more powerful foundation for the future (Risk Management Enterprise). The inquiry is no more whether to automate threat monitoring, it's how soon you can begin. To see the Riskonnect at work,
The response commonly copyrights on how well dangers are expected and managed. Project monitoring software program offers as the navigator in the tumultuous waters of project execution, offering tools that identify and analyze dangers and design methods to reduce them successfully. From real-time information analytics to extensive threat monitoring control panels, these tools offer a 360-degree sight of the project landscape, allowing job supervisors to make enlightened choices that keep their jobs on course and within budget.